SYSTEM SECURITY
This section lists software to encrypt information, securely erase files and filter and control internet usage.
INFORMATION
No extra information available at this time
|
|
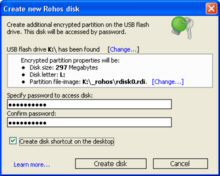
Rohos
Those who have megabytes of sensitive
files on their USB drive and are serious about data
security should not hesitate to use this tool.
|
|
|
|
True
|
|
|
Windows XP or above |
SafeSpace
Free for Home use. |
|
|
|
K9 Web
Free for Home use.
|
|
|
|
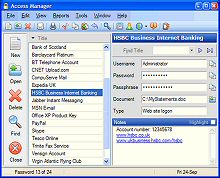
Access
|
|
|
|
KeePass
|
|
|
|
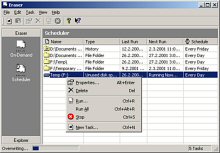
HD
Files that are erased using this program can not be recovered using undelete or any other recovery software.
|
|
|
|
Disk
|
|
|
|
CCleaner
|
|
|
VMWare Environment |
(VMware Analyzer)
|
|
|
|
Microsoft (Windows Analyzer)
|
|
|
Listed prices are correct at date of publication but are subject to availability or change without notice WARNING Click here to report a broken or incorrect link All images and trademarks remain the property of their respective owners E&OE |
||